Mirrors on the Dark Web 2/2
The most logical hypothesis is that of IP spoofing: the mirrors were created by someone who didn’t own the original sites. By generating their own copies of a site, the creator of the fraudulent site can obtain the logins and passwords of users who think they are connecting to the authentic site. When an e-commerce site is spoofed, the impersonator can even process payments on their own decoy website. In 2019, someone who created more than 800 decoys bragged about having earned more than 200 bitcoins (around 1.5 million euros at the time) by swindling customers of e-commerce sites on the dark web. This person revealed their fraud on the homepage of their decoy sites before disappearing.
It therefore seems likely that many of the mirrors on the dark web were created by one or several imposters. This proliferation of decoy mirrors is a major concern for the various dark web directories. After all, to be visible and accessible, these decoys must be referenced on sites that list domains on the dark web. Certain directories have tried to implement strategies to identify and stop referencing spoofed sites: some use their intuition while others rely on user feedback based on votes.
In November 2018, a person who was scammed six times on decoy mirrors decided to create a black list of spoofed sites: The Tor Scam List. This site allows users to report suspicious sites (“Submit a scam site”) and even remove sites that didn’t belong on the black list (“Report false listing”).
This initiative did not go unnoticed among the creators of fake sites. A year later, the first malicious mirror of the “Tor Scam List” was created. As the creator of the original site indicated on their page, scammers imitated the original site but added an extra section, “Verified sites”. This section, which claimed to list trustworthy sites, redirected users toward decoys.
Since that day, the site has been replicated 1,440 times, all malicious copies. And the epitome of sophistication, the creator(s) of these “tourist traps” on the dark web ensured that many of those sites are cross-linked. This makes them seem more credible. A user who wants to check the authenticity of a site might be tempted to check the consistency between several versions of the Tor Scam List. Since these decoys reference each other, the user falls into the trap, much like a spider’s web. In this case, there is a sort of reverse “web of trust”.
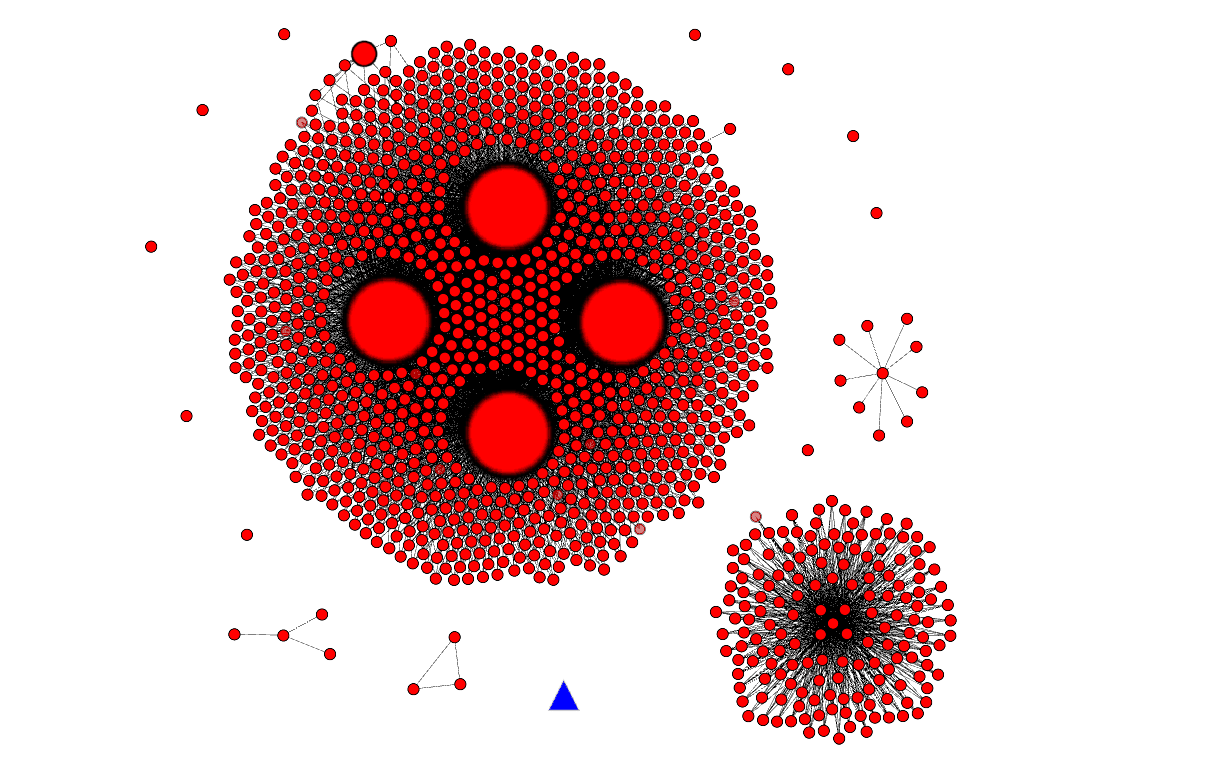
The following graph illustrates both the tenacity of the creators of malicious mirrors (red circles) and the relative weight of the original site (blue triangle). We can see two strongly interconnected networks and three networks with fewer connections. In the largest network, four nodes serve as a reference: their size is proportional to the number of links that redirect to these sites.
This is the clear irony of the dark web: not only is it largely made up of sites that scam people who imagine they can safely engage in fraudulent transactions, but the sites that are meant to denounce these scams have also been spoofed. However, this should not mask the very real and serious aspect of another part of the dark web. Alongside these mirrors, there are several thousand sites that we will soon examine in greater detail.